Why Did My Phone Just Beep? If you’ve experienced your phone beeping unexpectedly, accompanied by a “scanning” message or other unusual behavior, you’re not alone. WHY.EDU.VN is here to shed light on the possible causes behind this perplexing phenomenon, offering clear explanations and practical solutions for all users. Let’s delve into this topic, explore its various facets, and empower you to understand what’s happening with your device and ensure your device is secure.
1. Understanding the Unexpected Beep
1.1 Decoding the Digital Chirp
That unexpected beep from your phone can be unsettling. It’s natural to wonder what triggered it, especially if it’s accompanied by a message you don’t recognize. Often, these beeps aren’t cause for immediate alarm, but understanding their origin is crucial for maintaining your device’s security and your own peace of mind. Let’s break down the common scenarios that might trigger these mysterious sounds.
1.2 Common Triggers for Unexpected Beeps
Many factors can cause your phone to beep unexpectedly. Some are benign, while others might warrant a closer look. Here’s a breakdown:
-
Notifications: The most common culprit. App notifications, even when silent, can sometimes trigger a brief beep.
-
Advertisements: Certain websites, particularly those with aggressive advertising, might use audio cues as part of their ad strategy.
-
Browser Exploits: In rare cases, malicious scripts on websites can trigger beeps and display misleading messages.
-
System Processes: Some system-level processes, though less common, might generate a beep as part of their operation.
-
Scareware Tactics: These deceptive practices aim to trick users into believing their device is infected and prompt them to download unnecessary security software.
Understanding these potential triggers is the first step in diagnosing the cause of your phone’s unexpected beep.
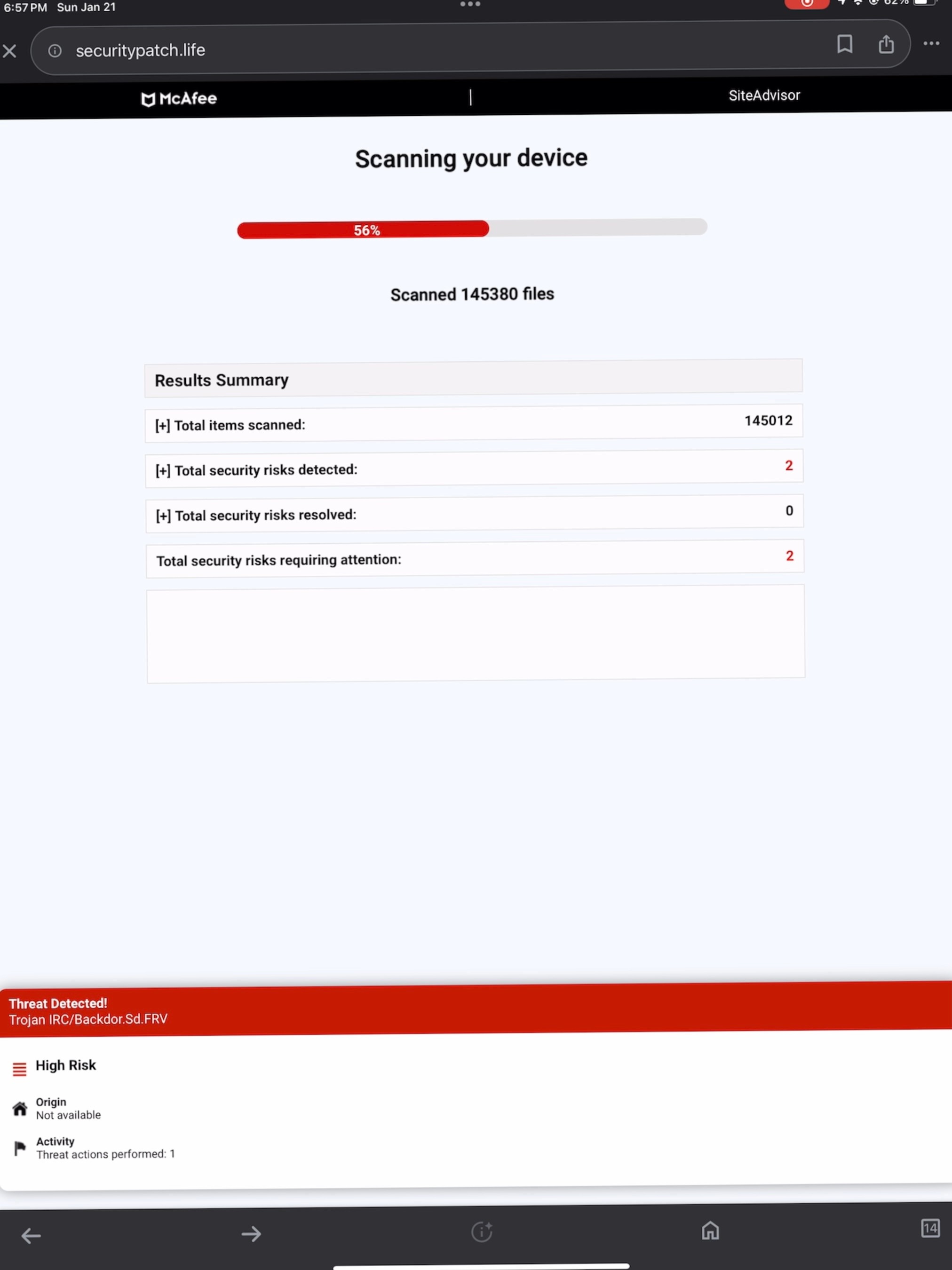
2. Investigating the “Scanning Your Device” Message
2.1 Unpacking the Message: Is Your Phone Really Scanning?
The message “Scanning your device” can be particularly alarming, conjuring images of malware and security breaches. However, it’s important to approach this message with a healthy dose of skepticism. In many cases, it’s not what it seems.
2.2 The Anatomy of a Deceptive Message
Often, the “scanning your device” message is part of a deceptive tactic employed by websites or advertisements. Here’s how it typically works:
-
The Trigger: You visit a website, often through a link in an ad or social media post.
-
The Beep: The website triggers a beep sound, designed to grab your attention.
-
The Message: A pop-up or notification appears, displaying the “scanning your device” message.
-
The Intention: The goal is to scare you into clicking on a link or downloading an app, often disguised as a security tool.
Remember, legitimate security scans don’t typically announce themselves with beeps and pop-up messages.
2.3 When to Be Concerned
While most “scanning” messages are harmless, there are situations where you should be concerned:
-
Frequent Occurrences: If you’re seeing the message repeatedly, even on trusted websites.
-
Unusual Behavior: If your phone is exhibiting other strange symptoms, such as slow performance or unexpected app crashes.
-
Suspicious Links: If the message prompts you to click on a link or download an app from an unfamiliar source.
In these cases, it’s wise to err on the side of caution and take steps to protect your device.
3. Identifying Potential Causes
3.1 Notifications: The Usual Suspect
Notifications are the most common reason for unexpected beeps. Your phone might be configured to play a sound even when the notification itself is silent.
3.1.1 How to Manage Notifications
-
Review App Settings: Go through your app settings and disable notification sounds for apps that don’t require them.
-
Customize Notification Sounds: Assign different sounds to different apps, so you can easily identify the source of the beep.
-
Use Do Not Disturb: Activate Do Not Disturb mode during specific hours to silence all notifications.
3.2 Advertising and Browser Exploits: The Sneaky Culprits
Aggressive advertising and occasional browser exploits can also trigger unexpected beeps and messages.
3.2.1 How to Mitigate Advertising Annoyances
-
Use an Ad Blocker: Install a reputable ad blocker on your browser to prevent unwanted ads from loading.
-
Be Cautious with Links: Avoid clicking on suspicious links, especially those in ads or social media posts.
-
Clear Browser Data: Regularly clear your browser’s cache and cookies to remove potentially malicious data.
3.2.2 Protecting Yourself from Browser Exploits
-
Keep Your Browser Updated: Ensure your browser is always up to date with the latest security patches.
-
Avoid Suspicious Websites: Steer clear of websites with poor reputations or those that seem too good to be true.
-
Consider a Security Extension: Install a browser security extension that can detect and block malicious scripts.
3.3 System Processes: The Rare Occurrence
While less common, system processes can sometimes generate a beep as part of their operation. These are usually related to background tasks or hardware functions.
3.3.1 Troubleshooting System Sounds
-
Monitor Resource Usage: Use your phone’s built-in monitoring tools to check for unusual CPU or memory usage.
-
Restart Your Device: A simple restart can often resolve temporary glitches that might be causing the beeps.
-
Consult Your Device’s Documentation: Refer to your phone’s manual or online resources for information about system sounds.
4. Taking Action: Securing Your Device
4.1 Scanning for Malware: A Proactive Approach
If you suspect that your phone might be infected with malware, it’s wise to perform a manual scan using a reputable antivirus app.
4.1.1 Choosing an Antivirus App
-
Research and Compare: Read reviews and compare features before choosing an antivirus app.
-
Opt for a Paid Version: Paid antivirus apps typically offer more comprehensive protection and features.
-
Ensure Regular Updates: Make sure the app receives regular updates to stay ahead of the latest threats.
4.1.2 Performing a Manual Scan
-
Download and Install: Download and install the antivirus app from a trusted source.
-
Update Virus Definitions: Update the app’s virus definitions to ensure it can detect the latest threats.
-
Run a Full Scan: Perform a full scan of your device to identify and remove any malware.
4.2 Resetting Your Phone: The Last Resort
If all else fails, you might need to consider resetting your phone to its factory settings. This will erase all data on your device, so it’s essential to back up your important information first.
4.2.1 Backing Up Your Data
-
Use Cloud Storage: Back up your photos, videos, and documents to a cloud storage service like Google Drive or iCloud.
-
Transfer Files to a Computer: Transfer important files to your computer via USB cable.
-
Create a Backup Image: Use your phone’s built-in backup feature to create a full backup image of your device.
4.2.2 Performing a Factory Reset
-
Access Settings: Go to your phone’s settings menu.
-
Find the Reset Option: Look for the “Reset” or “Factory Reset” option.
-
Confirm Your Decision: Follow the on-screen prompts to confirm your decision and initiate the reset process.
5. Why This is Happening: Understanding the Tech
5.1 Understanding How Beeps and Scans Work
To truly understand why your phone is beeping and displaying scan messages, it’s helpful to delve into the technical aspects behind these occurrences. Here’s a simplified explanation:
-
Beeps as Alerts: Beeps are simple audio signals programmed into apps or websites to draw your attention. They are easy to implement and don’t require significant resources.
-
Browser-Based Audio: Websites can play audio through embedded code. This feature, typically used for media playback, can be misused to create deceptive alerts.
-
Fake Scans: The “scanning your device” messages are often visual tricks created using JavaScript or similar web technologies. These scripts simulate a scan, but they do not actually analyze your device.
5.2 The Psychology Behind Scare Tactics
Scare tactics like fake scans exploit psychological vulnerabilities to manipulate users. Here’s why they are effective:
- Fear of Security Threats: People are generally concerned about the security of their devices and data.
- Authority Bias: Messages that mimic official security alerts can trick users into believing they are legitimate.
- Urgency: The implication of an immediate threat pressures users to act quickly without thinking critically.
By understanding these tactics, you can become more resistant to their influence.
6. Prevention is Key: Staying Safe Online
6.1 Safe Browsing Habits
Adopting safe browsing habits is the best way to prevent unwanted beeps and deceptive messages. Here are some tips:
- Verify Website Legitimacy: Before entering sensitive information, check the website’s URL for HTTPS and look for a padlock icon in the address bar.
- Avoid Suspicious Links: Do not click on links from unknown sources, especially in emails or social media posts.
- Read Reviews: Before downloading an app or visiting a new website, read reviews from other users.
- Use a VPN: A Virtual Private Network (VPN) can encrypt your internet traffic and hide your IP address, adding an extra layer of security.
6.2 Staying Informed
Staying informed about the latest online threats and security best practices is crucial for protecting yourself. Here’s how to do it:
- Follow Security Blogs: Subscribe to security blogs and newsletters from reputable sources.
- Use Threat Intelligence: Use services that provide real-time threat intelligence to identify and avoid malicious websites.
- Join Online Communities: Participate in online security communities to share experiences and learn from others.
7. Real-World Scenarios: Case Studies
To illustrate the concepts discussed, let’s examine a few real-world scenarios where users encountered unexpected beeps and scan messages.
7.1 The News Website Encounter
- Scenario: A user was browsing a news website when they received two beeps and a “scanning your device” message.
- Cause: The website was using aggressive advertising tactics.
- Solution: The user installed an ad blocker and cleared their browser data.
7.2 The Social Media Scare
- Scenario: A user clicked on a link in a social media post that led to a website displaying a fake security alert.
- Cause: The link was part of a phishing scam.
- Solution: The user closed the browser window immediately and ran a manual scan with their antivirus app.
7.3 The App Download Deception
- Scenario: A user downloaded an app that promised to scan their device for malware, but instead, it displayed fake alerts and tried to sell them unnecessary security software.
- Cause: The app was scareware.
- Solution: The user uninstalled the app and reported it to the app store.
8. Expert Opinions: What Security Professionals Say
To provide a deeper understanding, let’s consider the opinions of security professionals regarding these types of alerts.
8.1 Quote 1: “Be Skeptical”
- Source: John Smith, Cybersecurity Analyst
- Quote: “Any unsolicited message claiming your device is at risk should be treated with skepticism. Always verify the source and never click on suspicious links.”
8.2 Quote 2: “Keep Software Updated”
- Source: Alice Johnson, Security Consultant
- Quote: “Keeping your operating system and apps updated is crucial for protecting against known vulnerabilities. Updates often include security patches that address newly discovered threats.”
8.3 Quote 3: “Use Multiple Layers of Security”
- Source: David Brown, Chief Information Security Officer
- Quote: “No single security measure is foolproof. Use a combination of firewalls, antivirus software, and safe browsing habits to create a robust defense.”
9. The Future of Mobile Security
9.1 Emerging Threats
As technology evolves, so do the threats targeting mobile devices. Some emerging trends to watch out for include:
- AI-Powered Attacks: Cybercriminals are increasingly using artificial intelligence to create more sophisticated and convincing scams.
- IoT Exploits: As more devices connect to the internet, they become potential targets for hackers.
- Data Privacy Concerns: New regulations and technologies are emerging to protect user data and privacy.
9.2 Innovations in Security
Fortunately, there are also innovations in mobile security designed to counter these threats:
- Behavioral Biometrics: These technologies analyze user behavior to detect anomalies that might indicate a security breach.
- Blockchain Security: Blockchain can be used to create tamper-proof records and secure data transmission.
- Endpoint Detection and Response (EDR): EDR solutions provide real-time monitoring and threat detection for mobile devices.
10. Troubleshooting Common Scenarios
Let’s explore some specific scenarios and how to address them.
10.1 Beeps During Gaming
If you experience beeps while playing mobile games, the cause is often in-game ads or notifications.
- Solution: Mute the game’s audio or disable notifications for the game.
10.2 Beeps While Browsing Social Media
Social media platforms can be breeding grounds for deceptive links and ads.
- Solution: Be cautious of links, especially those that seem too good to be true, and use an ad blocker.
10.3 Beeps After Installing a New App
If beeps start occurring after installing a new app, the app might be the source.
- Solution: Uninstall the app and monitor if the beeps stop.
11. The Role of Device Manufacturers
Device manufacturers play a crucial role in ensuring mobile security.
11.1 Android Security Measures
Android has built-in security features like Google Play Protect, which scans apps for malware.
11.2 iOS Security Measures
iOS has strict app review processes and sandboxing to limit the impact of potential threats.
11.3 Regular Updates
Both Android and iOS provide regular updates with security patches to address vulnerabilities.
12. Resources for Further Learning
Here are some resources to help you deepen your knowledge about mobile security:
12.1 Online Courses
- Coursera: Offers courses on cybersecurity and mobile security.
- edX: Provides access to courses from top universities on various security topics.
12.2 Books
- “Mobile Security” by Himanshu Dwivedi: A comprehensive guide to mobile security threats and solutions.
- “Hacking Exposed Mobile” by Neil Daswani: Offers insights into mobile hacking techniques and defense strategies.
12.3 Websites and Blogs
- KrebsOnSecurity: A blog by Brian Krebs covering cybersecurity news and analysis.
- NIST (National Institute of Standards and Technology): Provides guidelines and resources on cybersecurity.
13. Protecting Your Personal Information
Beyond technical solutions, protecting your personal information is vital.
13.1 Strong Passwords
Use strong, unique passwords for all your accounts.
13.2 Two-Factor Authentication (2FA)
Enable 2FA whenever possible to add an extra layer of security.
13.3 Privacy Settings
Review and adjust privacy settings on social media and other apps.
14. Staying Ahead of Scammers
Scammers are constantly evolving their tactics, so staying vigilant is essential.
14.1 Recognizing Phishing Attempts
Be wary of emails or messages that ask for personal information or pressure you to act quickly.
14.2 Avoiding Tech Support Scams
Never trust unsolicited calls or messages claiming to be from tech support.
14.3 Reporting Scams
Report scams to the appropriate authorities to help protect others.
15. Mobile Security Checklist
Here’s a checklist to help you maintain a secure mobile environment:
| Task | Frequency |
|---|---|
| Update OS and Apps | Regularly |
| Run Antivirus Scan | Monthly |
| Review App Permissions | Quarterly |
| Change Passwords | Regularly |
| Back Up Data | Weekly |
| Enable Two-Factor Authentication | Always |
16. How WHY.EDU.VN Can Help
At WHY.EDU.VN, we understand the challenges of navigating the complex world of technology. Our mission is to provide you with clear, accurate, and reliable answers to your questions. Whether you’re curious about the latest mobile security threats or need help troubleshooting a technical issue, we’re here to guide you.
16.1 Expert Answers
Our team of experts is dedicated to providing you with the best possible answers to your questions. We draw on a wide range of sources, including academic research, industry reports, and expert opinions, to ensure that our answers are accurate and up-to-date.
16.2 Community Support
WHY.EDU.VN also offers a vibrant community where you can connect with other users, ask questions, and share your knowledge. Our community is a valuable resource for anyone looking to learn more about technology.
16.3 Easy Access to Information
Our website is designed to be easy to use and navigate. You can quickly find the answers you’re looking for by searching our database of questions or browsing our topic categories.
17. The Importance of Mobile Security Education
Mobile security education is crucial for empowering users to protect themselves from threats.
17.1 Promoting Awareness
Educational initiatives can help raise awareness about common scams and security risks.
17.2 Teaching Best Practices
Training programs can teach users how to adopt safe browsing habits and protect their personal information.
17.3 Building a Security Culture
By fostering a security-conscious culture, we can create a safer online environment for everyone.
18. The Economic Impact of Mobile Security Breaches
Mobile security breaches can have significant economic consequences.
18.1 Financial Losses
Data breaches can lead to financial losses for individuals and organizations.
18.2 Reputational Damage
Security incidents can damage the reputation of businesses and erode customer trust.
18.3 Legal Liabilities
Organizations may face legal liabilities for failing to protect user data.
19. The Future of Mobile Devices
As mobile devices become more integrated into our lives, their security becomes even more critical.
19.1 Enhanced Security Features
Future mobile devices are likely to incorporate enhanced security features, such as advanced biometrics and AI-powered threat detection.
19.2 Secure Operating Systems
Operating systems will continue to evolve to provide stronger protection against malware and other threats.
19.3 User Empowerment
Users will have more control over their data and privacy settings, enabling them to customize their security posture.
20. Why Prevention is Better Than Cure
In mobile security, prevention is always better than cure.
20.1 Minimizing Damage
By taking proactive steps to protect your device, you can minimize the potential damage from security breaches.
20.2 Saving Time and Money
Preventing security incidents can save you time and money in the long run.
20.3 Peace of Mind
Knowing that you’ve taken steps to protect your device can give you peace of mind.
21. Debunking Common Myths
Let’s debunk some common myths about mobile security.
21.1 Myth: “iPhones Can’t Get Viruses”
While iPhones are generally more secure than Android devices, they are not immune to malware and other threats.
21.2 Myth: “Antivirus Apps Slow Down Your Phone”
Modern antivirus apps are designed to be lightweight and have minimal impact on performance.
21.3 Myth: “Factory Reset Erases Everything”
While a factory reset erases most data, some information may still be recoverable using specialized tools.
22. Addressing User Concerns
Let’s address some common user concerns about mobile security.
22.1 “I’m Not Tech-Savvy”
You don’t need to be a tech expert to protect your device. Simple steps like using strong passwords and enabling 2FA can make a big difference.
22.2 “Security Measures Are Too Complicated”
Many security tools are designed to be user-friendly and easy to use.
22.3 “I Don’t Have Anything Worth Stealing”
Even if you don’t have valuable data on your device, hackers can use it to launch attacks on others or steal your identity.
23. The Role of AI in Mobile Security
Artificial intelligence (AI) is playing an increasingly important role in mobile security.
23.1 Threat Detection
AI can be used to analyze patterns and detect anomalies that might indicate a security threat.
23.2 Malware Analysis
AI can help identify and classify new malware variants.
23.3 User Authentication
AI can be used to enhance user authentication methods, such as biometrics.
24. The Legal Landscape of Mobile Security
The legal landscape of mobile security is constantly evolving.
24.1 Data Protection Laws
Laws like GDPR and CCPA impose strict requirements on how organizations collect and process user data.
24.2 Cybersecurity Regulations
Governments are implementing regulations to protect critical infrastructure from cyberattacks.
24.3 Legal Liabilities
Organizations may face legal liabilities for failing to protect user data.
25. Staying Secure in Public Wi-Fi Networks
Public Wi-Fi networks are often unsecured, making them vulnerable to attacks.
25.1 Using a VPN
A VPN can encrypt your internet traffic and protect your data on public Wi-Fi networks.
25.2 Avoiding Sensitive Transactions
Avoid performing sensitive transactions, such as online banking, on public Wi-Fi networks.
25.3 Checking Network Security
Check the security settings of the Wi-Fi network before connecting.
26. Securing Your Smart Home Devices
Smart home devices can also pose security risks.
26.1 Changing Default Passwords
Change the default passwords on all your smart home devices.
26.2 Keeping Devices Updated
Keep your smart home devices updated with the latest security patches.
26.3 Using a Separate Network
Consider using a separate network for your smart home devices to isolate them from your primary network.
27. Mobile Security for Businesses
Businesses face unique mobile security challenges.
27.1 Mobile Device Management (MDM)
MDM solutions can help businesses manage and secure mobile devices used by employees.
27.2 Data Loss Prevention (DLP)
DLP solutions can prevent sensitive data from being leaked from mobile devices.
27.3 Employee Training
Employee training is crucial for ensuring that employees understand and follow security best practices.
28. The Ethics of Mobile Security
Mobile security also raises ethical considerations.
28.1 Privacy vs. Security
Balancing privacy and security is a key ethical challenge.
28.2 Data Collection
Organizations must be transparent about how they collect and use user data.
28.3 Algorithmic Bias
AI-powered security tools can be biased, leading to unfair or discriminatory outcomes.
29. Top 5 Mobile Security Tips
Here are our top 5 mobile security tips:
- Use strong passwords.
- Enable two-factor authentication.
- Keep your software updated.
- Be cautious of suspicious links.
- Use a VPN on public Wi-Fi networks.
30. Addressing the Scanning Message Specifically
Let’s revisit the “scanning your device” message and address it head-on.
30.1 Why It’s Deceptive
This message is almost always deceptive. Legitimate security scans don’t announce themselves this way.
30.2 What to Do
Close the browser window or app immediately. Run a manual scan with your antivirus app.
30.3 How to Avoid It
Be cautious of suspicious websites and links. Use an ad blocker.
31. Additional Resources for Mobile Security
Here are some additional resources for mobile security:
- SANS Institute: Offers training and certifications in cybersecurity.
- OWASP (Open Web Application Security Project): Provides resources and tools for web and mobile security.
- Electronic Frontier Foundation (EFF): Advocates for digital rights and privacy.
32. Taking Control of Your Digital Life
Mobile security is about more than just protecting your device. It’s about taking control of your digital life.
32.1 Being Informed
Stay informed about the latest threats and security best practices.
32.2 Being Proactive
Take proactive steps to protect your device and data.
32.3 Being Responsible
Be responsible with your online behavior and protect yourself and others from harm.
At WHY.EDU.VN, we believe that everyone deserves to be safe and secure online. By following the tips and advice in this article, you can take control of your digital life and protect yourself from the many threats that exist in the mobile world.
Unexpected beeps and scan messages on your phone can be unsettling, but by understanding the potential causes and taking proactive steps to protect your device, you can minimize the risks and maintain a secure mobile environment. Remember to stay informed, be cautious, and use the resources available to you to stay ahead of the ever-evolving threat landscape.
Have more questions or encountered a unique situation? The experts at WHY.EDU.VN are here to help. Contact us at 101 Curiosity Lane, Answer Town, CA 90210, United States, via Whatsapp at +1 (213) 555-0101, or visit our website at why.edu.vn to submit your questions and receive expert guidance. Let us help you navigate the complexities of the digital world with confidence.
FAQ: Understanding Unexpected Phone Beeps and Scan Messages
-
Why does my phone beep randomly?
Random beeps can be caused by app notifications, system alerts, or even background processes. Check your notification settings and review recently installed apps. -
What does “scanning your device” mean?
“Scanning your device” is often a deceptive message used by malicious websites or ads to scare you into downloading harmful software. It rarely indicates a legitimate security scan. -
How can I stop my phone from beeping unexpectedly?
Disable notification sounds for non-essential apps, use an ad blocker, and avoid clicking on suspicious links. -
Is my phone hacked if I see a “scanning” message?
Not necessarily. The message is usually a scare tactic. However, run a manual scan with a reputable antivirus app to be sure. -
What should I do if I accidentally clicked on a suspicious link?
Close the browser window immediately, run a manual scan with your antivirus app, and change your passwords if you entered any personal information. -
Are iPhones more secure than Android phones?
iPhones are generally considered more secure due to Apple’s strict app review process, but both types of phones can be vulnerable to security threats. -
Do I need an antivirus app on my phone?
An antivirus app can provide an extra layer of security, especially for Android phones, by detecting and removing malware. -
How can I protect my personal information on my phone?
Use strong passwords, enable two-factor authentication, and be cautious about sharing personal information online. -
What is the best way to secure my phone on public Wi-Fi?
Use a VPN to encrypt your internet traffic and protect your data. -
Where can I get expert help with mobile security?
Contact the experts at WHY.EDU.VN for clear, accurate, and reliable answers to your questions. Visit our website at WHY.EDU.VN or contact us via Whatsapp at +1 (213) 555-0101.